- Transcripts
-
Transcripts are generated using a combination of speech recognition software and human transcribers and may contain errors. Please check the corresponding audio before quoting in print.
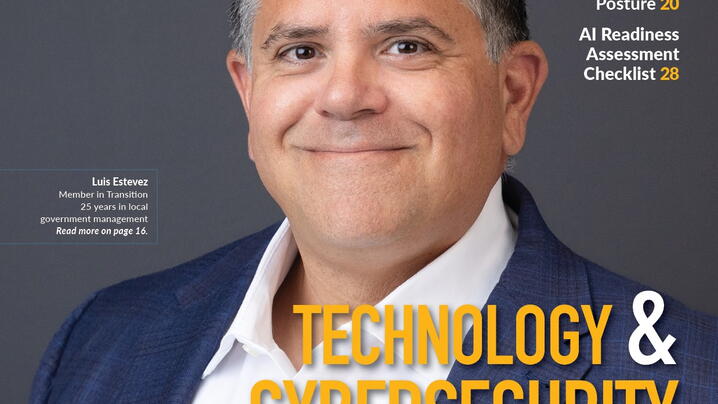
Joe Supervielle: Welcome to Voices in Local Government, an ICMA podcast. With me today are Parham Eftekhari and Hemant Desai. Parham is the executive director of the Cybersecurity Collaborative, a community of security executives and board chair of the Institute for Critical Infrastructure Technology, a leading cybersecurity think tank based on Washington DC. Hemant recently joined ICMA as chief information officer and had the same role in local government with Guilford County, North Carolina. Thanks for joining us today.
Parham Eftekhari: Hey, it's great to be here.
Hemant Desai: Glad to be here. Thank you.
Joe Supervielle: For the audience, this is our first cybersecurity episode. We are planning on more with maybe a rotating cast of guests and experts. So if you have questions, suggestions on specific subtopics you want us to dive deeper into or even interested in participating as a guest yourself, please reach out on ICMA Connect, the website anyway, you can get ahold of us. There'll be some more contact information on the podcast webpage. So let's get right into it, guys. Cybersecurity, the unique and difficult challenge to local government and really all businesses face, there's no endpoint necessarily, there's no finish line. This is an ongoing task. Everyone has to keep up with all the time. So just to start with, if you could each give us your initial take on it and the quick version on where you think this topic is with local government, what people are currently doing, what we could do a little bit better, and then we'll get into some more specifics. Parham, please go ahead and kick us off there.
Parham Eftekhari: Great. Joe, thanks again. And Hemant, it's great to be here with you. I think in general, what we're seeing right now is a continued increase in the topic of cybersecurity and in the importance of cybersecurity as it relates to local government as well as just the private sector in general. Of course, everyone's aware of the significant rise in ransomware threats. I think that can be attributed to both this impact of the pandemic and the rapidly changing ecosystem that organizations are tasked with protecting. Just in general, if you take a step back even more plainly, there's more technology out there. Organizations and local governments are reliant on increasing numbers of third parties to deliver services, all of whom are using technology that are oftentimes logically connecting into the network and the adversaries are becoming more sophisticated in how they're exploiting vulnerabilities in our networks.
So all of this is just compounding the challenge that we face, which is how do we take the limited resources that we have with respect to people and money and prioritize what we need to do to improve the defenses of our local government, organizations and all of our partners. So it's a very important topic and I don't see that changing any time in the near future.
Joe Supervielle: Sure. And Hemant, you've been on both sides of it, working on the local government. Audience might be people who were in your role as the chief information officer or the city managers themselves, senior department heads. So give us your insight on being in that hot seat.
Hemant Desai: So thank you again. Glad to be here. So one of the things, and I think to add to what Parham said, Parham brought very interesting points that as more and more proliferation of different devices that people use now to connect and the fact that being in government agencies, there's going to be much more public scrutiny if you will, on cybersecurity related incident. A lot of people may not know that equal number of companies may also be impacted. So security awareness from cybersecurity perspective is more of an incremental growth and mindset. So in government agencies that Parham actually said, what I faced, even when I was accounting, is that you always had limited budgets. Financial budgets, but also resource limitations on number of people that are going to be manning the store, if you will, of your security infrastructure.
So you can never keep up with the threats. And I think part of challenge that I'm seeing, and more and more C level executives and government agents are going to be faced with this, that parameter will not change. We'll always be constrained in resources if not financial, also. So the challenge is how do you make sure that you strengthen the most important asset, which is the people that work in the organization. And the more awareness, and I know we're going to get to that shortly, we, as IT leadership, can spread the awareness across multiple layers of organizational assets, human assets. Then I think the evolution of security infrastructure will change from bottom up because right now organizations still unfortunately think that by beefing up the top layer, which is putting more appliances hiring consultants, which is important, putting infrastructure in third party's hand; those are all good first and second measures. But the bottom line is people in your organization and government agents are learning that the more you spread the awareness, I think the better we can strengthen up security posture.
Joe Supervielle: Okay. So one phrase I've heard you both use before is layered security. If a city manager came to both of you and said "The basic stuff's there, we're aware of this, we know we need to do better, but what's next?" What is the highest priority in each of your mind?
Parham Eftekhari: First of all, when it comes to layered security, I think the most important thing to remember is that there is no silver bullet to addressing security. And as you, Joe, mentioned in your opening remarks, that this is a continuous process. You don't do security once and then are good until next year. It's a culture change and requires, to Hemant's point, that security awareness and training as well as technical and non-technical controls. I think if a local government or city leader came to me and said, "How can I prioritize, given limited resources, whether it's human resources or budget?" I think what you can do is first look and ask, are you doing what we often refer to as you know, basic cyber hygiene? Do you have your patch management in place? Do you have a good program to manage identity access management and following the principle of least privilege? Do you have the basic firewalls in place?
And very important as part of, I think basic cyber hygiene, is having a well thought out security awareness and training program that is repeatedly engaging with the community and with the organization and really working to change the culture. I think once you have that down, then you can start to think about layering on more advanced capabilities. But depending on the requirements of your organization, there isn't one answer that fits all. But I think you really want to start with the basic blocking and tackling in terms of cyber hygiene, making sure you have the security awareness training program, and then you can layer on additional capabilities that may be more advanced. I think there's a misconception out there that you need a lot of money to do security. It helps. It's all obviously very nice to have money. I don't want to negate the importance of financial support, but there is a lot of impact that can be had on the security of an organization just by implementing policies and governance and some basic things that are available I think to most organizations.
I think, Hemant, and I'd love to hear your thoughts on this. I think given that you've played this role, I think he touched on this; it's the so important for the all the right stakeholders in an organization to collaborate. And so you got to get the CIO, your CTO, your compliance people, your legal people, HR. And of course, all the elected officials. All these folks need to have a role in this security. Can't just do it on its own. So part of it's just getting the right folks involved.
Hemant Desai: Absolutely. In fact, to piggyback off of that, Joe, what Parham said absolutely is so true, that having a basic cybersecurity or cyber hygiene, as he mentioned, rightfully so, it's just a starting point. That having a principle of least privilege, firewalls, MFA, multifactor authentication, those are just companies that don't already have those things are already way behind and more and more companies are already making those the high priority and they've already implemented those and they're on their way to getting that part taken care of. I think for me, what helped me the most when I was on the other side in a different county implementing these cybersecurity measures is, having a strong top level leadership at all levels. Because as you know, government agencies or even in businesses, I would say that would be true too, that our customers, my customers in different county, or my internal departments. So their day to day jobs cannot be impacted by what we... And I think that oh, you cannot do certain things because it's not safe. It doesn't make sense to them because they've been always doing that before.
So by just us saying it to them doesn't mean that it's going to be embraced. So oftentimes what I learned is, and more and more agencies I think are doing that, is leveraging internal resources. But again, I was privileged. I had top down support from my county management administration all the way down, even up to the board of directors and board of commissioners. Bottom line is, top level support is important, obviously, but leveraging other resources. So I was in a task with working with risk management. So making sure that you get your risk management department involved to help you assess your cybersecurity or your risk awareness score. How much are you willing to give up?
And then you assess your risk and then start assigning, as Parham rightfully said, appropriate resources. Not just financial resources, but ongoing education. Top level support from county management downwards, but also making sure that you leverage partnership with other departmental stakeholders in spreading the cyber hygiene. And it's an incremental process. It didn't happen overnight even for us in different county. As you keep increasing awareness, more and more department stakeholders will start supporting the endeavor because they see that you are ultimately trying to protect the county assets, the citizens' assets. And I think ultimately the messaging and relaying that message on ongoing basis made a big difference, certainly for me, in that evolutionary process of two or three year timeframe to trend in a security posture.
Parham Eftekhari: If I can add on to that, I think one of the keys to engaging senior leadership and getting their buy-in, it's really important that you're speaking in a language that they understand and talking to their priorities. At the end of the day, if the person, whoever's listening right now in the audience, if you're an IT person or a security person or a risk person, your priorities and your focus is on something completely different than what most senior leadership is. You're there to take care of that for them. And so when you want to get buy-in from senior leadership, going to them and talking to them about the attack vector or the technical controls you want to put in place and how it'll protect endpoints and things, that's not going to resonate. But if you schedule, for example, a couple hours with the group and go through a simulation and say, "Here is the consequences to our community if these systems get taken out, if this data gets stolen, if our systems get ransomware. Here are the repercussions on the organization. Here's the repercussions on you and how it'll impact you personally."
Once you go through that and help them understand what this actually would look like, then what will often happen is they'll say, "Gosh, what do we need to do to prevent this?" And then you can say, "What we need is, in very non-technical terms, we need X, Y, and Z." And I think that's a very effective way to go about building that census and getting by. It's communication and the way in which you communicate and what you communicate is critical to be successful in this.
Joe Supervielle: Yeah. You just said the communication between the leadership, city manager, whatever it might be, and the technical people, the technical side cannot assume that everyone else understands that language. It's important to start with the why's and the motivating factors to get that leadership on board. I guess I would take it a step further. So what would either of you say to, let's say a city manager is listening right now and they say, "I believe it. I'm convinced. My CIO already convinced me. I'm trying to set a good example, but my staff, whether it's a hundred people or a few thousand people, there's still that segment who just view it like "That's IT's problem. I don't want to do this training. I don't want to do X, Y, or Z," because they're all busy trying to do their day to day job and they own responsibilities.
Especially when there is a larger staff, it's hard to get 100%. So it might be impossible. What do you recommend to them if that's a struggle? The manager already knows that this needs to happen, but they're just not seeing the movement on the bigger staff buying in and taking it seriously.
Hemant Desai: Yes. If I may, so one, it's a very, very good question, Joe. We often face that even where I was in my prior environment. So part of the challenge that we always face in IT is that you'll never get, as you say, 100% participation because people always say, "I don't have time for the training," or "This is not relevant for me," or "This is a nuisance."
Joe Supervielle: Or they click through it without really paying attention, which I may or may not have done myself before.
Hemant Desai: Yes. Exactly. And so that happens to best of us and it can happen to even IT folks too. And it's happened to IT folks too, in the past. The important thing is having a clear mandate from top that there are consequences of not following through the best practices. Not consequences because you clicked on something that you shouldn't have. There shouldn't be any penalty for mishaps, if you will. But there certainly should be a mandate of expectation that if and when that does happen and there's a training program in place, that there is a full support from top level that it'll be followed through. Given reasonable time so that staff members don't feel that "This is just a nuisance or it's optional." Because that's when it starts becoming more of, "Hey, training is just a formality. It's a checkbox for internal audit or for risk management," which is also important, but that's not what we are doing it for. We're doing it because it has consequences to a larger team, to the larger environment.
So I think mandate from top down and then following up at the departmental level and the each individual team level implementing it. And as Parham rightfully said, communicating the why and making it more palatable in their language. Because oftentimes, and we are all guilty and I'm guilty of that too, oftentimes in IT, where we start talking and showing those bar charts of how many hacks have happened, that doesn't mean anything to end user because it's, what's in it for me syndrome, which we all are attune to. So we've got to speak in that term, show them the why's of "Here's what will happen in reality, and here's what has happened in reality with XYZ organization." And I think that's helped a lot.
Joe Supervielle: Yeah. We've seen the headlines of local governments or specific business with the ransomware and it doesn't usually end well with those stories. Also, the non-leadership non-IT person maybe would do well to realize that it's not these scams or the way the bad guys will come and get in. It's not like the old email scam with the "Prince needs your help to get the money out." That's a joke from the late nineties. It's much more sophisticated than that, more complicated, more versions of it. And although the training, it is a hassle, I think people could justify that, I also think it does a good job explaining not just the what to do, but here's what to look for and why it's important.
So Hemant, you also earlier, you said a risk score. I wanted to get back to that a little, a little bit. How is that implemented? It's a hard thing because the success can't just be measured by, "Oh, we haven't had a massive incident." How does the security officer or the chief information officer measure progress or checkpoints as they go implementing more of this layered security and more of these priorities? How can the city manager who doesn't necessarily understand all the technicalities of it, understand if their team is doing a good job or not?
Hemant Desai: That again, a very good question. So have a clear guideline of measurement. So for example, having a clearly written down incident response, IRT, as we call it, plan. IRT plan, which has a clear guideline of what are some of the steps you're going to take if and when some incident were to happen. But you mentioned risk management. One of the things that we did was created literally a risk register, which listed all the different systems. Not just hardware systems, but processes and systems that were either exposed or that could be potentially exposed to cybersecurity threats. Then we assigned a score. Assigned some type of a score. There was a collaborative effort between departmental stakeholders and IT. Then we started measuring how implementing security posture, the strengthening security postures improved the security score. So for example, in a specific department, not naming them, where they were more prone to being triggered happy and clicking on emails or spams. So then we give them more education, what happens when that happens and providing them a visual report of the progress over time.
And showing them that their systems, for example, if the systems include healthcare information, that how that information now has been protected because they did not do certain actions, which otherwise would've caused compromise of the healthcare data, for example. So giving them a visual measure, almost coming back to what Parham said, talking in their language and being more proactively communicative, but showing them actual measures. And in our case, what I meant by that is, that literally we had a risk of register with clearly defined measures within each department with their systems. So now if I'm talking to you and UN public health, I'm showing you that your five systems had the following security threats in the last one month. And I show them, and they said, "Wow, I didn't know that," I said, "Exactly," but we stopped that because you helped us in the overall process. So the risk scores were lower and lower, which means the security vulnerability decreased dramatically over a period of one or two years.
Joe Supervielle: And that's where the theoretical 100% is not the goal. It's just to lower the risk as much as possible.
Hemant Desai: Yeah.
Joe Supervielle: Parham, do you want to add anything to just the whole idea of how you measure whether it's the internal team or even if it was a consultant that a smaller community who doesn't have that knowledge at all, maybe on staff.
Parham Eftekhari: Yeah, absolutely. I think Hemant brought up some great points. I think it's just a different way of looking at it. To piggyback off of what he said, developing a plan, either you have to be able to have specific goals and measurable targets regardless of what it is, whether it's the scenarios that Hemant described, whether it's on securing the number of endpoints that you have, whether it's on doing training and simulation on certain cases, essentially, what an organization or what a local government wants to do is whenever they do the strategy planning, look at it and say, "The next year, here are our goals. We want to do a complete inventory of our endpoints and refresh that once a year. And then once we understand what our network looks like, then we want to ensure that we apply endpoint protection on X percentage or on the ones that are classified as high as risk."
If you first want to build out a plan based on your requirements, based on your resources, you're not setting yourself up for fail. And I think you can, in that plan that set milestones, whether they're percentages, metrics, date goals, probably a mix of all the above, and then to systematically work it. And I think that goes back to how Joe, how you started the conversation. This is an iterative process. When you're building out your security program, you're going to start, let's say on year one, with a certain amount of goals and a certain amount of resources. And in theory, what should happen is that every year, then you're going to build on it and build on it and build on it. Hopefully part of that process and one of your first priorities is getting buy-in from different stakeholders. That should hopefully lead to additional resources.
It's unrealistic to think that if the listener out there has a security program, that you go to accomplish vast amount things and processes and implementations in year one, even in year one and two, to make a plan, set some goals, maybe develop a 3, 4, 5-year plan and see what you want to accomplish each year. And then go ahead and slice it up, make it manageable, and then you can execute and measure against it. I think having that plan is really critical. And by line of work, you mentioned, I work with a lot of chief information security officers. The ones who are very successful and the ones who seem to be making significant impact to their organizations, it all starts with their roadmap and their vision to how they want to prioritize their actions based on their resources and based on their risk and their environment and compliance and all those things. You build a plan and you execute against it. So you shouldn't go willy nilly at this, just be very methodical. And I think it'll help in both the measurement and the overall success of the program.
Joe Supervielle: Putting myself in the hypothetical city manager shoes, is there a way, whether I'm talking to my current CIO or CIS or whatever the title is versus maybe even trying to hire someone new because we're a mess and we need to start at the beginning. How can a manager judge that or understand real differences versus maybe too much of that technical talk? Because earlier you said that the key is communication. And a good professional and technical side knows how to speak to the manager and in their own language. But if I'm the manager and I can't get that out of anyone, how do I translate? How do I even know what to do next if I'm not understanding what anyone's telling me? What would you recommend to that person if they asked you, "Hey, I don't understand any of the things these people are telling me. It seems like a sales job or just all hype. I don't know what's real"? What's their next move?
Parham Eftekhari: That's a great question. I think, I think first of all, the first thing to do is that city manager should turn back around to whoever tasked with security and articulate that and say, "Look, I am hearing everywhere that there are major digital threats that could be impacting us. I've asked you to report on it and I've asked you to manage it, and I need you to change the way you're communicating." And I think that in and of itself, the ability for the city manager to go back and just articulate that they are interested, this is a priority, but they're having trouble understanding it, they just need to work through that process together. I have utmost faith and confidence in the IT and security leaders in local government. But if there's a city manager listening and they're saying that to their person, and they're not getting the response that they need, and they're doing coaching and everything, at the end of the day, this is serious stuff. And so then you have to make a decision of, "Is that the right person tasked with the security function?
Do I need to give it to a different person? Do I need to swap the role out?" But I think that if there's communication barriers, that the city manager should take it back to that per person and say, "Look, I need to understand better." And maybe give them some guardrails to say, "Here's how you can explain it to me. Explain to me the risks, explain to me how it'll impact tax revenue." I don't know, whatever they think and whatever the priorities are. Maybe more descriptive in what you're looking for. And then you'll get the data that'll align with how it is that you can translate to make better decisions.
Joe Supervielle: Okay. Hemant, I could flip that around. What if the CIO is doing the most they can with what the resources, financial and manpower otherwise, and their city manager is, not indifferent, but just like, "Okay, well, I don't understand this. So that's what I hired you for. So go do it, but they're not maybe giving you that buy-in or support that Hemant, you were describing earlier. How can the CIO role navigate that with someone who ultimately is their boss? Maybe you are doing a good job of explaining it in real terms and not the tech talk, but it's still not really making a dent or really getting in there. How would you recommend the technical person change the strategy or change their approach to try and get through to the city manager?
Hemant Desai: Very good point. So I would say that about five to seven years ago, Joe, that used to be the norm, in the sense that that scenario played out much more frequently, a few years ago because the support at the top level was little less. Let's say they were not as serious about cybersecurity because they truly felt that, "It's somebody else. It doesn't affect us. It won't affect us." Until it was my job to keep saying that in cybersecurity and IT security, it's not a question of if. It's a question of when. And I kept saying that, they never believed me that it's not whether if we get compromised, it's when, so how do you minimize the risk, as I mentioned earlier, which begins with communication, but to come back to your question, if it's still happening and maybe some organizations, smaller entities may still be facing the top level's, maybe lack of support, what I would recommend is what did even when I was not getting full support. Not intentionally, but because there was not much awareness seven years ago of that type of thread. It's building your foundation from bottom up.
So if you have a good relationship with your stakeholders, and coming back to what Parham said, communicating at all levels, which is what, ultimately among other things, IT manager's and director's job is. Not just the familiar top most level, which is obviously important because he or she is your boss, but also building relationship at departmental and even staff levels to make sure that they trust you. They understand you. They know your message is meant for not just stopping people from doing their job, but from protecting the assets, the very assets that they are responsible for. I think easier said than done. I'll be the first to confess, it didn't just happen overnight. It was an iterative process, as we talked earlier. It took continuous effort on my part, but I would say full credit to my team. I still remember when I first joined the county, we had a team of one person in security. Just one person and me, so two people, for staff and a county of half a million plus people. We were not the only ones, other agencies have similar challenges.
And then as awareness spread, the support came from top down and beefed up and they're in much better shape now. So I think your question is well formed that it necessarily exists where people don't have support, but it is still the IT director's job to build that foundation bottom up.
Joe Supervielle: Yeah. And what I'm hearing is there's no shortcut or magic sentence you can say to that city manager. It's just the grind of earning the trust and earning the support and earning the "Okay, not only are we taking this seriously, but we're actually going to start doing the action items to make it happen."
All right. I appreciate both your time today. Again, this topic could go on for hours and hours. So we are planning on some follow up episodes again to the audience. You can send specific questions in on anything we covered today, anything you want us to cover in the future. If you're interested in participating yourself, we want to hear from a lot of different voices. The podcast page will have some additional resources, including the cybersecurity collaborative. So thanks for Parham's help with that. And Hemant, welcome to ICMA, we're happy to have you. Any parting words of wisdom for the managers or IT people out there on this topic before we sign off on this episode?
Parham Eftekhari: Yeah. I'll chime in and Hemant, pass it to you. I think the most important thing is don't be intimidated and develop a plan even if it's looking to make incremental, modest steps forward and just start to check things off the box. A lot of resources out there. A lot of free resources out there, from CISA and DHS and FBI and groups like the cybersecurity collaborative. So take advantage of those. And reach out; the cybersecurity community is very supportive. And if you reach out to folks even just people you meet on LinkedIn who are maybe in your same space in your community, find cyber experts wherever you are, and say, "Look, I'm tasked with building the security program for my organization. Can we grab coffee and just talk about where to begin?" Don't be afraid. You'll find a very supportive community out there that really understands the national security implications of what it is that you're doing and will want to help.
Hemant Desai: Yes, I would certainly echo what Parham said. Follow the cybersecurity basic hygiene, day to day stuff, cybersecurity professionals have to do, but also make sure that you have a plan in place like Parham said, and then have a strategy to implement the plan but also reinforce cybersecurity awareness completely from top down and bottom up on a regular basis. So I think if you keep doing that, keep maintaining your hygiene, awareness training, and then building the bottom of support is going to be a tricky process. It's going to be an evolutionary process, but at some point you'll keep getting more and more mature in your cybersecurity space. And hopefully at some point that there'll be that mix of risk mitigation, risk avoidance, where you feel that you have at least some level of cybersecurity posture that you can live with, that you don't feel threatened on every single moment of your daily business workflow, if you will.
Joe Supervielle: All right. Thanks again. Hemant, I promise to take my next mandatory training more seriously instead of multitasking during a meeting. I learned my lesson. And I have to admit they got me. I think it was right before you joined, but I did get the test or email. It was internal but it was the fake test email, which in regular Outlook is pretty easy to identify. I feel like I'm good at that, but I was on my phone after work hours just trying to catch up on email, the three year old pulling on me, asking me to play. And of course, I'm distracted. And I see the note from HR and I click on it. As soon as I'm clicking on it. I'm like oh no, click out. Too late. They got me. So we can all do better, staff included. It's not just the top of the cybersecurity force or the city manager. All the local government staff need to do their part too. So thanks again guys for your knowledge today. We'll be back with another episode in a few weeks.
Hemant Desai: Thank you very much. Thank you for that.
Parham Eftekhari: Thank you, Joe.
Joe Supervielle: Bye
Guest Information
Parham Eftekhari, Executive Director, Cybersecurity Collaborative
Hemant Desai, Chief Information Officer, ICMA
Episode Notes
Parham Eftekhari and Hemant Desai discuss the universal threat of cyber-attacks and the unique challenges local governments face as high-profile targets, including:
- What are best practices?
- What do we prioritize?
- How can we train a reluctant staff?
- How to translate between a city manager and the CTO role?
- How can we demonstrate urgency to gain more resources?
- What are realistic and measurable goals beyond did we suffer a major attack or not?
Resources:
ICMA Cybersecurity Leadership Academy