by Xavier Hughes, Chief Technology and Innovation Officer, ICMA
It’s 11:20 p.m. I’m about to go to sleep, when suddenly, I receive what appears to be an urgent email from ICMA Executive Director Marc Ott. The email reads:
“Hi Xavier, are you available? I need you to personally run a task for me ASAP. I'm caught up in meeting now. Just reply my email. Let me know if you can get this done for me right now. Sent from my iPad”
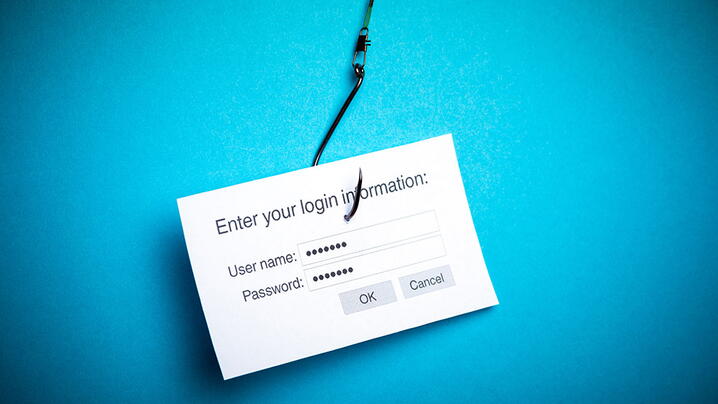
My first instinct is to immediately reply, to ensure that my boss has everything he needs. But then, suddenly, I step on the brakes. My cybersecurity training kicks in and I begin to inspect the email. I quickly realize that the sender’s email account is not Marc’s – neither his ICMA work account, nor his personal one.
The originator’s email address was a clear example of cyber phishing. I immediately went on an emergency notification spree.
I first notified my engineering and customer success team. I then notified Marc, and the rest of our leadership team. Finally, I notified our entire workforce, letting them know that there was a strong possibility that they also might be targeted. They had. And by then, several of our hardworking co-workers had fallen victim to the shrewd tactics of our attackers.
I had so many questions running through my head. How could this have happened? How did they get through our security protocols? How is it that several of my co-workers fall for this Machiavellian cyber campaign?
At ICMA, we use all kinds of products and services to protect ourselves from cyber-attacks. In the spirit of transparency, I am going to share a summary of all of them – please take a look:
- Barracuda Email Security Service Essential. All emails from external senders to recipients in our domains go here first. Barracuda screens for SPAM and malware. It also has settings to detect flaws with Sender Policy Framework (SPF), DMARC, and DKIM protocols. And it allows us to block or exempt specific senders, mostly by address or IP.
- Barracuda Sentinel. Emails that pass through the first layer get screened by Barracuda Sentinel to detect PHISH attacks. If it suspects a PHISH, it routes the email to the recipient’s Junk folder and sends them and us an alert with details. Sentinel also monitors mailboxes for suspicious activity.
- Office 365. Emails delivered by Barracuda get screened by O365 for SPAM and malware. Suspect emails are quarantined, the recipient gets an email with options to release SPAM emails and allow or block the sender.
- KnowBe4. Cyber security education and testing. We have trainings for staff, and ongoing PHISH campaigns to test them.
- Comodo Endpoint Management. Antivirus, anti-malware, patch management, remote control of computers.
- Cisco Umbrella . Network traffic screening, protects against known suspect websites and domains.
The deeper we dug, the more we realized that, simply put, we had to significantly increase the level of cybersecurity training offerings to our co-workers. So, here is what we decided to do:
- Reset all account passwords and asked all co-workers to log in and create new ones.
- Leveraged an all-hands meeting to discuss the intrusion, evidence to date, plan ahead, and critical nature of cyber security.
- Immediately scheduled cyber security training for all staff.
- Formulated a couple of cyber security tests via KnowBe4 (see below for more details).
Since then, we have not experienced any cyber intrusions, but the fight is not over. We continue to push our cybersecurity training agenda, and have begun looking at additional things we could do to further protect our workforce and platforms.
As we continue on this journey, we will make sure to share our lessons learned, strategies and tactics to combat this ever-changing issue. For now, I will leave you with a collection statistics and resources to learn more about phishing, its consequences, and best ways to stay safe.
Who is being “phished”?
- According to PhishMe’s Enterprise Phishing Resiliency and Defense Report, phishing attempts have grown 65% in the last year.
- According to Wombat Security State of the Phish, 76% of businesses reported being a victim of a phishing attack in the last year.
- According to the Verizon Data Breach Investigations Report, 30% of phishing messages get opened by targeted users and 12% of those users click on the malicious attachment or link.
- According to the SANS Institute, 95% of all attacks on enterprise networks are the result of successful spear phishing.
- According to Symantec, phishing rates have increased across most industries and organization sizes — no company or vertical is immune.
- According to the Webroot Threat Report, nearly 1.5 million new phishing sites are created each month.
What is the cost of phishing?
- The average financial cost of a data breach is $3.86m (IBM)
- BEC scams accounted for over $12 billion in losses (FBI)
What can I do right now to prevent a successful phishing attack?
- Educate your employees on what phishing is, how it is commonly carried out, and what to look for. They should also know what to do when they fall victim to a phishing scam, such as knowing who to notify or alert. This should be an on-going training – with updated information about new phishing methods.
- Evaluate how vulnerable you are. There are a lot of software products now that allow you to simulate a phishing attack. These software applications will send a mock phishing e-mail to your employees and then show you statistics on who fell prey. This process can also help you know how effective your training is.
- Install all the necessary protections, such as having an antivirus and antimalware software installed. If possible, make sure that SPAM and other e-mail filters are in place. This way, you help minimize the number of phishing attempts that goes through your employees.
- Establish security policy in place that includes everything – including setting up a strong password and encouraging employees to change their password often.
- Encrypt your company's sensitive information will help. Cybercriminals might social engineer their way to getting their hands-on confidential files, but if it is encrypted, they will have a harder time reading it.
- Consider disabling HTML e-mails and using only text e-mails.
- Require additional encryption for employees who work outside the office.
- Institute a Web filter that will block out phishing sites.
- Activate two-factor authentication. With this in place, you can be sure that even if a hacker is able to get your employee's user name and password, they still would not be able to access their e-mail accounts and other resources.
Where can I learn more?
- What is Phishing? http://www.phishing.org/what-is-phishing
- Phishing Techniques: http://www.phishing.org/phishing-techniques
- 10 Ways to Avoid Phishing Scams: http://www.phishing.org/10-ways-to-avoid-phishing-scams
- Phishing Quiz: http://www.phishing.org/how-phish-prone-are-you
Be safe out there.
Xavier
New, Reduced Membership Dues
A new, reduced dues rate is available for CAOs/ACAOs, along with additional discounts for those in smaller communities, has been implemented. Learn more and be sure to join or renew today!
